Educational assessment data breaches affected 28% of UK institutions in 2025, yet many CIPD training providers underestimate their security obligations. Assessment records contain sensitive personal information requiring robust protection under UK GDPR and Data Protection Act 2018. This guide equips educators and assessment professionals with practical strategies to secure CIPD qualification data, meet JCQ standards, and implement technical safeguards that protect both institutional integrity and candidate privacy while maintaining efficient marking workflows.
Table of Contents
- Key takeaways
- Understanding the legal framework for data security in UK educational assessments
- Core technical safeguards: encryption, access control and system security
- Managing cyber risks: phishing threats, staff training and incident recovery
- Balancing proctoring integrity and privacy in CIPD assessments
- How EduMark supports secure and compliant CIPD assessments
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Legal framework and DPIAs | UK GDPR and the Data Protection Act 2018 govern CIPD assessment data processing and DPIAs are required for high risk processing. |
| Privacy by design | Privacy by design must be embedded from the assessment design stage with encryption, role based access controls and retention policies. |
| Core technical safeguards | Encryption protects data at rest and in transit using standards such as AES 256 and TLS 1.3. |
| Staff training and governance | All staff with access to assessment data must receive regular training on security policies breach reporting and confidentiality, with annual refresh and documented records. |
| Proctoring privacy safeguards | Proctoring enhances assessment integrity but organisations must safeguard candidate privacy by minimising data collection and conducting DPIAs before deployment. |
Understanding the legal framework for data security in UK educational assessments
UK educational institutions processing CIPD assessment data must comply with UK GDPR and Data Protection Act 2018 requirements covering student records, assignment submissions, and results. These laws mandate lawful processing grounds, data minimisation, accuracy, confidentiality, and accountability for every stage of assessment handling.
Data Protection Impact Assessments (DPIAs) are legally required when processing creates high risks to candidate rights and freedoms. Assessment centres must document these assessments before implementing new marking systems or proctoring technologies. DPIAs identify potential privacy risks and establish mitigation measures, creating an auditable trail that demonstrates compliance to the Information Commissioner's Office (ICO).
Privacy-by-design principles must be embedded from the assessment design stage. This means incorporating encryption, role-based access controls, and data retention policies into workflows before collecting candidate information. Reactive security measures applied after data collection begins leave institutions vulnerable to breaches and regulatory penalties.
Staff training on personal data handling is not optional. Every team member accessing assessment data requires regular instruction on security policies, breach reporting procedures, and confidentiality obligations. Training must be documented and refreshed annually to maintain awareness.
Legal responsibilities for assessment centres:
- Establish lawful basis for processing assessment data before collection
- Implement technical and organisational measures proportionate to risk
- Maintain records of processing activities and security incidents
- Appoint a Data Protection Officer if processing is large-scale
- Respond to subject access requests within one month
- Report qualifying breaches to ICO within 72 hours
Pro Tip: Schedule DPIA reviews every six months and update data protection policies immediately after regulatory changes to avoid ICO fines that can reach £17.5 million or 4% of annual turnover.
Assessment providers using AI-assisted CIPD marking platforms must verify that these systems incorporate privacy-by-design and maintain compliance documentation accessible for audits.
Core technical safeguards: encryption, access control and system security
Encryption protects assessment data both at rest (stored on servers or devices) and in transit (moving between systems or users). Encryption standards such as AES-256 for storage and TLS 1.3 for transmission prevent unauthorised access even if systems are compromised. Without encryption, stolen devices or intercepted network traffic expose candidate information immediately.

Role-based access control (RBAC) limits data visibility to personnel with legitimate educational interests. A marker reviewing Level 5 CIPD assignments should not access Level 7 candidate records or administrative financial data. RBAC systems assign permissions based on job function, creating audit trails that track who accessed which records and when.
Physical security remains critical despite digital transformation. Paper assignment submissions, backup drives, and server rooms require controlled access, visitor logs, and environmental monitoring. A locked filing cabinet is insufficient; assessment centres need alarmed storage areas with restricted key or card access.
| Security measure | Implementation method | Primary benefit | Limitation |
|---|---|---|---|
| Encryption at rest | AES-256 on storage devices | Protects data if hardware stolen | Requires key management |
| Encryption in transit | TLS 1.3 for network traffic | Prevents interception during transfer | Does not protect endpoints |
| Role-based access control | Permission groups by job function | Minimises insider risk exposure | Needs regular permission audits |
| Multi-factor authentication | Password plus biometric or token | Blocks unauthorised login attempts | User resistance to complexity |
Essential technical controls:
- Deploy endpoint protection on all devices accessing assessment systems
- Enable automatic security updates for operating systems and applications
- Implement network segmentation isolating assessment data from general systems
- Maintain comprehensive audit logs with tamper-evident storage
- Conduct penetration testing annually to identify vulnerabilities
- Establish secure disposal procedures for retired hardware containing data
Pro Tip: When selecting third-party marking platforms, verify they provide SOC 2 Type II reports or ISO 27001 certification demonstrating comparable encryption and access standards to your internal controls.
Regular security testing validates that technical safeguards function as designed. Quarterly vulnerability scans and annual penetration tests identify weaknesses before attackers exploit them. Assessment centres should treat security testing as essential maintenance, not optional expenditure.
Managing cyber risks: phishing threats, staff training and incident recovery
Phishing attacks remain the top threat to educational institutions, with 82% of breaches involving human error or social engineering. Attackers impersonate senior staff, examination boards, or technology vendors to trick employees into revealing credentials or transferring sensitive assessment data. A single successful phishing email can compromise entire marking systems.
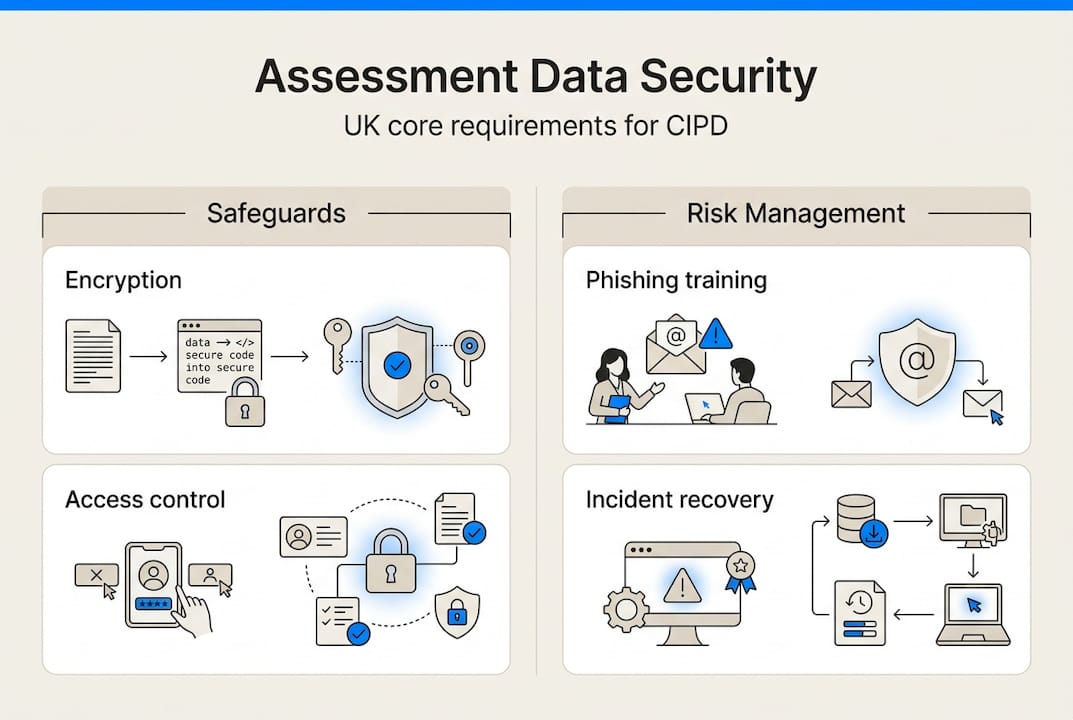
JCQ mandates annual cyber security training for all staff handling examination materials, including assessment centres processing CIPD qualifications. Training must cover phishing recognition, password hygiene, incident reporting, and physical security protocols. Centres must maintain training records and hardware asset registers documenting every device used for assessment activities.
Web filtering blocks access to malicious sites and prevents staff from inadvertently downloading malware. Combined with regular software patching, filtering reduces attack surface area significantly. Assessment centres should implement filtering at network level rather than relying on individual device settings that users can disable.
Disaster recovery planning ensures business continuity when breaches or system failures occur. Recovery plans must specify backup frequency, restoration procedures, alternative marking arrangements, and communication protocols. Testing recovery procedures annually validates that backups are viable and staff understand their roles during incidents.
"Over a quarter of UK education institutions experienced cyber security breaches in 2025, with phishing as the primary attack vector. Institutions that suffered breaches reported average costs of £3,500 and significant reputational damage affecting student recruitment."
Cyber security best practices:
- Conduct simulated phishing exercises quarterly to test staff awareness
- Require complex passwords changed every 90 days for assessment systems
- Implement email authentication protocols (SPF, DKIM, DMARC)
- Establish clear incident response procedures with designated coordinators
- Maintain offline backups stored separately from primary systems
- Review and update disaster recovery plans after every drill or real incident
Pro Tip: Embed phishing awareness into monthly team meetings using real examples from education sector breaches, making security discussions routine rather than annual events that staff forget.
Assessment centres using AI-assisted CIPD marking benefit from platforms that incorporate security monitoring and automated backup procedures, reducing the burden on internal IT resources while maintaining protection standards.
Balancing proctoring integrity and privacy in CIPD assessments
Online proctoring technologies monitor candidates during remote assessments to detect potential misconduct. Three primary methodologies exist: AI-assisted automated monitoring, asynchronous review of recorded sessions, and live human proctoring via webcam. Each approach presents distinct security and privacy considerations for CIPD qualification providers.
AI-assisted proctoring uses algorithms to flag suspicious behaviours such as looking away from screen, additional people in room, or unusual typing patterns. These systems generate alerts for human review rather than making final integrity decisions. However, biometric data collection and continuous monitoring raise significant privacy concerns requiring careful data protection compliance.
Asynchronous proctoring records entire assessment sessions for later review by trained staff. This method provides flexibility for candidates across time zones but creates large volumes of video data requiring secure storage and clear retention policies. Providers must document how long recordings are kept and who can access them.
Live proctoring involves real-time human monitoring, offering immediate intervention capability but requiring significant staffing resources. Privacy implications are similar to asynchronous methods, with additional concerns about proctor discretion and potential bias in real-time decision-making.
| Proctoring method | Security strength | Privacy risk | Resource requirement |
|---|---|---|---|
| AI-assisted automated | High detection coverage | Biometric data concerns | Low ongoing cost |
| Asynchronous review | Thorough post-assessment analysis | Large video storage needs | Moderate review time |
| Live human proctoring | Immediate intervention | Real-time surveillance concerns | High staffing cost |
| Browser lockdown only | Limited to technical controls | Minimal personal data | Low implementation |
Ethical proctoring considerations:
- Apply data minimisation by collecting only necessary monitoring information
- Provide transparent candidate information about monitoring methods and data use
- Obtain explicit informed consent separate from assessment registration
- Implement retention policies deleting proctoring data after results are finalised
- Consider accessibility needs and provide alternative arrangements for candidates unable to use standard proctoring
- Conduct DPIAs specifically for proctoring systems before deployment
Assessment integrity and candidate privacy are not mutually exclusive. CIPD providers can achieve both by selecting proportionate monitoring methods, being transparent about data practices, and respecting candidate rights throughout the assessment process. Excessive surveillance that collects biometric data without clear justification violates UK GDPR principles and damages institutional trust.
How EduMark supports secure and compliant CIPD assessments
Navigating data security requirements whilst maintaining efficient marking workflows challenges many CIPD training centres. AI-assisted CIPD assignment marking platforms address this by embedding security controls directly into assessment processes. EduMark provides encryption for submitted assignments, role-based access ensuring only authorised markers view candidate work, and comprehensive audit trails documenting every interaction with assessment data.
The platform's infrastructure meets UK GDPR requirements through regular security audits, data protection impact assessments, and transparent privacy policies candidates can review before submission. Automated workflows reduce human error risks whilst maintaining the essential human oversight that ensures fair, consistent marking aligned with CIPD standards. Centres benefit from CIPD marking technology that accelerates turnaround times without compromising the data protection standards regulators and candidates expect. Integration with existing assessment workflows means centres can adopt secure marking solutions without disrupting established processes or requiring extensive staff retraining.
Frequently asked questions
How can educational institutions ensure compliance with UK GDPR in assessments?
Conduct Data Protection Impact Assessments before implementing new assessment systems or proctoring technologies. Embed privacy-by-design principles including encryption and access controls from the initial planning stage. Train all staff handling assessment data regularly on security policies and breach reporting procedures. Document processing activities and maintain records accessible for regulatory audits.
What are the best practices to defend against phishing in educational settings?
Implement mandatory annual cyber security training covering phishing recognition and reporting procedures. Conduct quarterly simulated phishing exercises to test staff awareness and identify training gaps. Deploy network-level web filtering to block malicious sites and email authentication protocols to prevent spoofing. Ensure software patches are applied promptly across all systems accessing assessment data.
How do assessment centres balance online proctoring with candidate privacy?
Adopt data minimisation by collecting only monitoring information necessary for integrity verification. Provide clear, transparent explanations of monitoring methods and data use before candidates begin assessments. Use ethical AI tools that flag suspicious behaviour for human review rather than making automated decisions. Obtain explicit informed consent separate from general assessment registration and implement retention policies deleting proctoring recordings after results are confirmed.
What should providers check when working with third-party assessment software vendors?
Verify vendors hold relevant GDPR compliance certifications such as ISO 27001 or SOC 2 Type II reports. Ensure signed Data Protection Addenda are in place specifying data handling responsibilities, security standards, and breach notification procedures. Review vendor disaster recovery capabilities and backup procedures. Confirm vendors conduct regular penetration testing and provide transparent incident response processes. Avoid common data protection pitfalls by documenting vendor due diligence thoroughly before contract signature.